Pharmacy and drug manufacturing
This report brought to you by Intrinsec’s Research & Invistigation CTI Team
Also available on
What’s in the report ?
Core findings include
- Strategic and tactical analysis of cyber threats targeting the pharmacy and drug manufacturing sector, with a focus on ransomware attacks, threat actors, and geographic distribution.
- Covers significant third-party and supply chain risks, including OAuth abuse, vishing campaigns, and exploitation of vulnerabilities impacting healthcare organizations worldwide.
- Detailed ransomware group activity is analyzed, highlighting top intrusion groups, the sectors they target, and countries most affected by attacks.
- Includes case studies of compromised entities, vulnerability exploitations like SAP NetWeaver and others, plus ongoing credential-stealing campaigns affecting pharmacy systems.
- Concludes with actionable recommendations for security measures, such as auditing access, enforcing multifactor authentication, monitoring dark web mentions, and strengthening supply chain defenses.
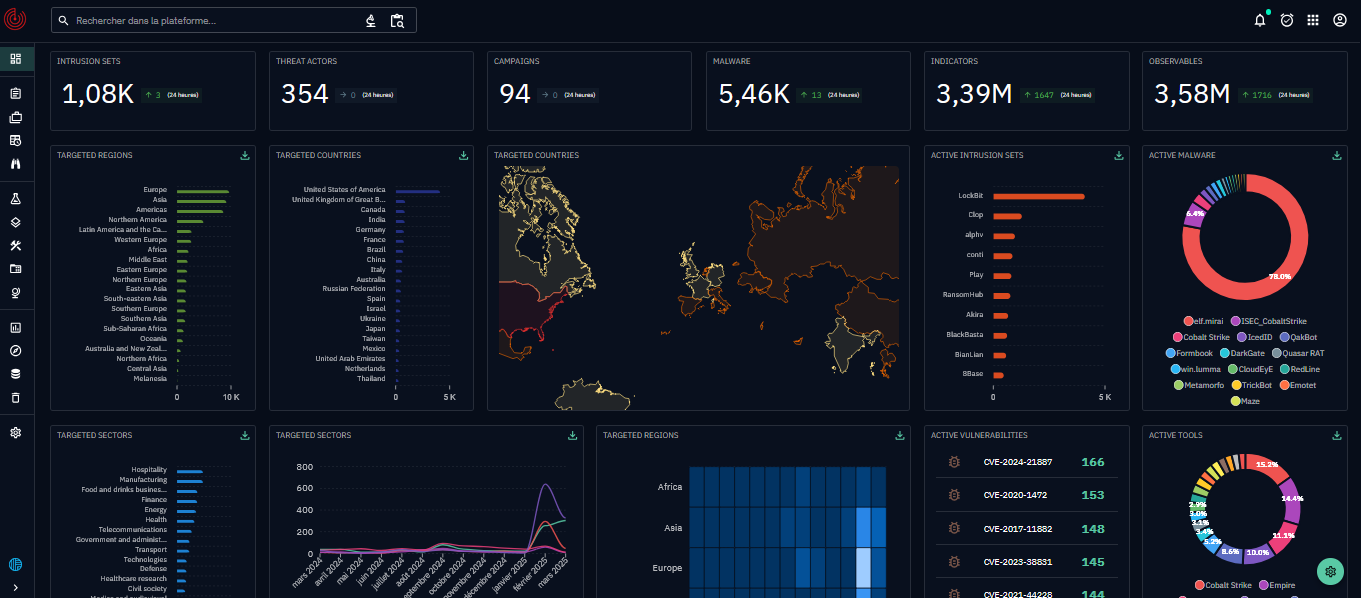
Try Our X-TIP Platform today
Explore detection and anticipation capabilities in real time with Intrinsec’s managed Cyber Threat Intelligence platform, X-TIP.
Actionable resources included in this report
Practical cyber threat intelligence assets to strengthen detection, response, and strategic decision‑making for your organization.
Downloadable IOC List:
Full list of dynamic Indicators of Compromise (domains, IPs, emails) associated with the Pakistani syndicate.
Incident Response Recommendations:
Step-by-step mitigation guidelines for security teams: detection, hardening, user awareness, and threat hunting.
Briefing Slides & Visuals:
Key visuals and OSINT pivots allowing you to trace similar infrastructure in your own context.
Ongoing Updates:
Follow Intrinsec’s latest findings with our CTI feed and regular sector-specific digests.
About Intrinsec’s CTI Team
This “Threat Intelligence Report” is developed by Intrinsec’s Cyber Threat Intelligence (CTI) Team – experts in global cybercrime tracking and analysis. With years of experience supporting European critical sectors and Fortune 500 companies, the team specializes in actionable threat intelligence, advanced investigation (hunting, reverse, pivots, darkweb), and crisis response.
Our reports are based on unique intelligence feeds, incident response cases, and proprietary investigation methods, giving our clients early warnings and deep context for emerging threats.


